Anarchy is back. The last time anarchy was a noticeable political movement in the world, bomb throwing anarchists were killing heads of state and government leaders, as part of their scheme to take the whole system down, and impose socialist rule. Of course they claimed socialist rule didn’t really count as rule, because ideology.
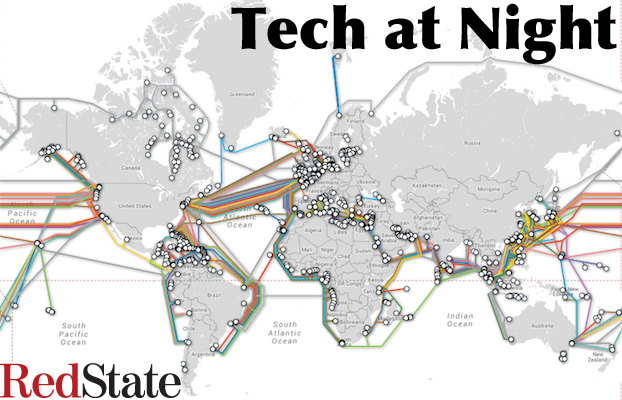
Well, these days world leaders are much better protected, so instead the anarchists are going after websites and just trying to disrupt, particularly online. We must be mindful of this, create cybersecurity policies that let government and industry share information (through bills like CISA), and make sure to investigate and prosecute these crimes.
Continue reading »

The Global Warming fraudsters have to cheat their data in order to ‘hide the decline’ of temperatures. Likewise, it’s turning out that the left is going to have to cheat in order to make it look like American Internet competition is terrible. they’re going to do this by cheating the definitions by changing them mid-stream, in order to create a decline. Liars all, the Net Neturality/Universal Broadband left.
Uf you want to see the truth though, it’s Net Neutrality that actually harms Internet access, as seen in Chile.
Continue reading »
We missed Tech on Monday because of Memorial Day, but I was sick anyway so it wasn’t happening. Still getting over my cold though, so this tech is about 2 hours late.
Here’s your periodic reminder that kids and teenagers shouldn’t be online unsupervised. Adult sexual predators are actively hunting them to take advantage of them.
Keeping data Internet-accessible is inherently dangerous to your privacy. Internet security is spotty but still users don’t actually quit services that gather their data, as their outrage is always short lived. People want convenience and innovation so I reject calls for bigger government to try to use FTC to enforce a privacy few actually want.
Continue reading »

If you want an explanation of the ‘Heartbleed’ bug in the news, Francis Cianfrocca gives a good explanation in Coffee and Markets. But more important is his point about NSA. He always speaks carefully about that organization, but in his roundabout way he made an excellent point: NSA has a dual mandate. NSA’s job is both to break into enemy communications, and to protect our communications. The Heartbleed bug is so devastating that if they knew about it, they’d have to work to protect us from it, before someone else could use it against us. That’s how bad it is. There’s no way they knew about it a year.
If you don’t like that businesses hire lobbyists, shrink government and quit picking winners and losers so they don’t have to.
Continue reading »

They told us for years that Mitt Romney was a terrible person because of his ties to private equity. Now Julius Genachowski, Obama’s first FCC chair is going into private equity, and not a peep from the radicals.
Erick Erickson’s already covered all the reasons Peter King should be excluded from polite political society, but I just want to remind as well that Rand Paul’s grandstanding isn’t all that great. Snowden is an unrepentant criminal and traitor and it’s a shame that Paul is just sucking up to his father’s crazier fans. I guess he really wants their campaign donations more than he wants his dignity.
Continue reading »

The argument for the ECPA (email warrant law) reform in a nutshell: because a lot of people store important data on other people’s servers, we need to tighten warrant laws for that data. I don’t buy the necessity, especially with FISA also under attack. If terrorists have data on Google’s servers, I want Google to be able to hand over that data. But this idea is popular and I expect it to pass eventually.
I called it: China cut Bitcoin’s access to the Chinese banking system, just as the US cut online gambling access to the US banking system (and like the US did after the freezing of Mt. Gox’s Dwolla account. Result: Bitcoin prices are tumbling, even if firms like Bank of America can’t assume it’s going to go away.
I wish it would though, since Bitcoin continues to be a magnet for crime.
Continue reading »